Short Notes: Computer Networks
Netwok Models, IP Addressing and TCP/IP
Application Architectures and Protocols
There are 2 possible structure of applications working over the internet:
-
client-server server: always-on host, permanent IP address, data centers for scaling clients: communicate with server, may be intermittently connected,may have dynamic IP addresses do not communicate directly with each other
-
peer-to-peer (p2p) no always-on server; arbitrary end systems directly communicate; peers request service from other peers, provide service in return to other peers self scalability – new peers bring new service capacity, as well as new service demands; peers are intermittently connected and change IPn addresses; complex management.
-
FTP: separate control, data connections FTP client contacts FTP servermat port 21, using TCP client authorized over control connection, client browses remote directory, sends commands over control connection when server receives file transfer command, server opens 2 nd TCP data connection (for file) to client after transferring one file, server closes data connection server opens another TCP data connection to transfer another file control connection: “out of band” FTP server maintains “state”: current directory, earlier authentication
-
Emails The Simple Mail Transfer Protocol (SMTP) is an application used by mail servers to send, receive, and relay outgoing email between senders and receivers. SMTP is intended to be used on top of the Transmission Control Protocol (TCP), which guarantees reliable delivery of the individual packets that make up a conversation. An outgoing mail server is a generalized term to describe a system that collects, processes, and serves email. Much like a mail carrier, every email message passes through the mail server before reaching its destination. SMTP is a push protocol and is used to send the mail whereas POP (post office protocol) or IMAP (internet message access protocol) is used to retrieve those emails at the receiver’s side. The SMTP model is of two types:
End-to-End Method Store-and-Forward Method The end-to-end model is used to communicate between different organizations whereas the store and forward method is used within an organization. An SMTP client who wants to send the mail will contact the destination’s host SMTP directly, to send the mail to the destination. The SMTP server will keep the mail to itself until it is successfully copied to the receiver’s SMTP. SMTP is a mail delivery protocol, not a mail retrieval protocol. Mail Transfer Agent (MTA): The server runs a program called a Mail Transfer Agent (MTA). The MTA checks the domain of the recipient’s email address, and if it differs from the sender’s, it queries the Domain Name System (DNS) to find the recipient’s IP address. This is like a post office looking up a mail recipient’s zip code. Usually, this first email server is not the actual email’s final destination. The server, having received the email from the client, repeats this SMTP connection process with another mail server. That second server does the same, until finally the email reaches the recipient’s inbox on a mail server controlled by the recipient’s email provider. The Internet Message Access Protocol (IMAP) and Post Office Protocol (POP) are used to deliver the email to its final destination. The email client has to retrieve email from the final mail server in the chain in order to display the email to the user. The client uses IMAP or POP instead of SMTP for this purpose.
POP The Internet Message Access Protocol (IMAP) and Post Office Protocol (POP) are used to deliver the email to its final destination. The email client has to retrieve email from the final mail server in the chain in order to display the email to the user. The client uses IMAP or POP instead of SMTP for this purpose. POP3 downloads the original emails from the email server on a single device/computer. Then it deletes the emails from the server’s inbox. It lacks synchronization; thus, several devices cannot access the same email. This protocol is best suited for people who use a single device (say office computer) to access emails.
IMAP IMAP (Internet Message Access Protocol) is also an email retrieval protocol to retrieve email messages from the server. IMAP4 is the latest version in use.
IMAP is the most commonly used email protocol. After establishing the connection with the server, IMAP retrieves all the data from the mail server and caches the retrieved data on your local device. It allows you to access the same email on different devices since all your data is stored on the server and not on the local machine. Any changes you make to the emails will be synced to the mail server.
Networking Models
| OSI Model | TCP/IP Model | |
|---|---|---|
| 1 | Short for “Open system Interconnect” | Short for Transmission Control Protocol/ Internet Protocol |
| 2 | Conceptual Model; generic and protocol independent standard | Client-Server model, commonly used model to communicate over internet; based on standard protocols |
| 3 | 4 layers | 7 layers |
| 4 | Transport Layer is Connection Oriented | Transport Layer is both Connection Oriented and Connection less |
| 5 | Follows vertical approach | Follows horizontal approach |
| 6 | Developed by ISO (International Standard Organization) | Developed by DoD (the Department of Defense |
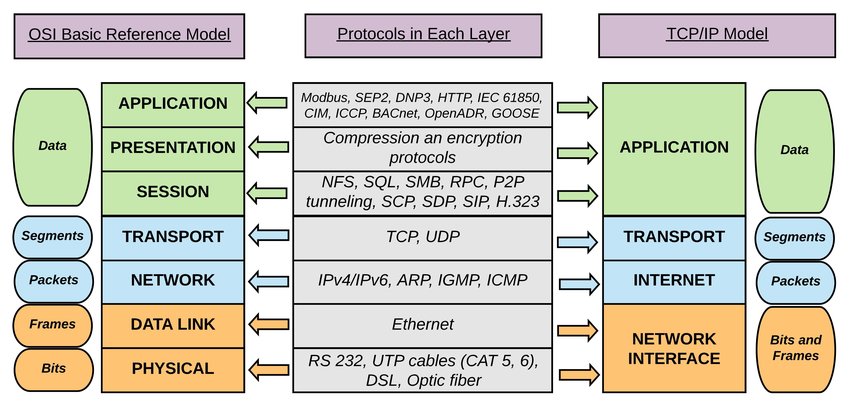
Layers of OSI model:
- Application Layer: Users can access the network by using interfaces and services like electronic mail, shared database management, file access/transfer and the other services.
- Presentation Layer: Focuses on the syntax and semantics of the transmitting information. Performs tasks such as translation, encryption and compression.
- Session Layer: Establishes the session between different machines in order to synchronize and maintain the interaction between them.
- Transport Layer: Performs service point addressing, connection control, segmentation and reassembly, flow control and error control.
- Network Layer: Performs Logical addressing and routing; translates the network logical address into physical MAC address so that the two systems residing in the different networks could also communicate efficiently.
- Data Link Layer: Makes the physical layer free from error by masking them so that the network layer does not notice them. Tasks carried out in the data link layer are framing, access control, physical addressing, error and flow control.
- Physical Layer: It transmits the individual bits over the transmission channel. The physical layer deals with the description of the characteristics of the interface between the devices and the transmission media, representation of bits, synchronization of the bits, data rate, physical topology, line configuration, transmission mode.
Layers of TCP/IP Model:
- Network Interface Layer: Acts as an interface between hosts and transmission links and used for transmitting datagrams. It also specifies what operation must be performed by links like serial link and classic ethernet to fulfil the requirements of the connectionless internet layer.
- Internet Layer: Transmit independent packets into networks; Includes the IP (Internet Protocol), ICMP (Internet Control Message Protocol) and ARP (Address Resolution Protocol) as the standard packet format for the layer.
- Transport Layer: Enables a fault-free end-to-end delivery of the data between the source and destination hosts in the form of datagrams. The protocols defined by this layer are TCP (Transmission Control Protocol) and UDP (User Datagram Protocol).
- Application Layer: Permits users to access the services of global or private internet. The various protocols described in this layer are virtual terminal (TELNET), electronic mail (SMTP) and file transfer (FTP). Some additional protocols like DNS (Domain Name System), HTTP (Hypertext Transfer Protocol) and RTP (Real-time Transport Protocol). The working of this layer is a combination of application, presentation and session layer of the OSI model.
IP Addressing:
Classful IP Addressing
- Classful addressing is how the early Internet was formed.
- IP assignments were given on the Octet boundaries.
- Led to a lot of wasted IP addresses. If, for instance, you only needed 300 IP addresses, a Class C would not suffice, so you would end up with a Class B and nearly 60,000 IP addresses would be wasted.
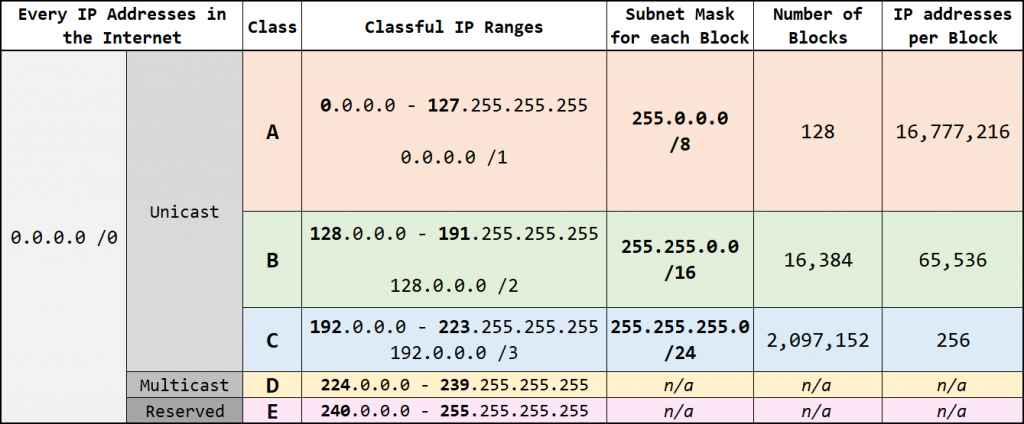
Classless Inter-Domain Routing (CIDR)
- IP assignments not limited to 3 classes; whole unicast range can be allocated in any size block.
- Slash (/) notation adopted for network masks.
- IP address ranges are assigned with a much, much smaller rate of wasted IP addresses.
- Eg. If you need 500 IP addresses … You also get a
/23. - If you need 1000 IP addresses … You get a
/22.
- Eg. If you need 500 IP addresses … You also get a
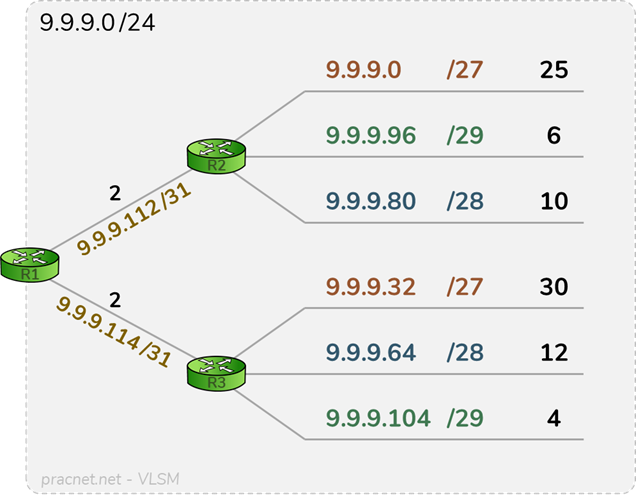
Fixed Length Subnet Masks (FLSM)
- Every network within an infrastructure is the same size.
- Every Subnet in the topology must be the same size. i.e. if one Subnet needs to be a
/27, then all Subnets need to be a/27. - Example: You are assigned by your RIR this
/24:9.9.9.0/24. Since the biggest segment of the networks requires 30 IP addresses, the smallest size subnet that can be utilized is a/27, which contains 32 total IP addresses and 30 usable IP addresses.
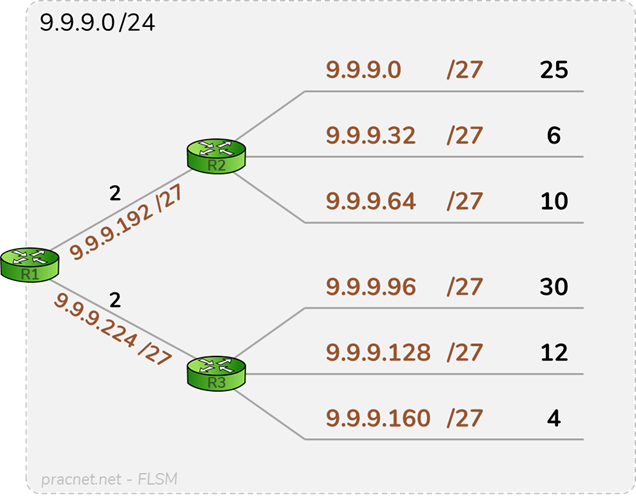
In this particular topology, a total of 91 IP addresses is required, but the entire /24 (256 IP addresses) was allocated, leaving no additional room for expansion. This is a very inefficient utilization of the assigned IP address space.
- This was done to save bits on the wire. The early, early routing protocols (i.g.,
RIPv1and its predecessors) saved bits on the wire by not included the subnet mask in advertisements — the subnet mask for all advertised networks was assumed to be the same mask assigned to the receiving interface.
Variable Length Subnet Mask (VLSM)
- Allows all subnet masks to be variable sizes.
- Similar to FLSM, but much more efficient.
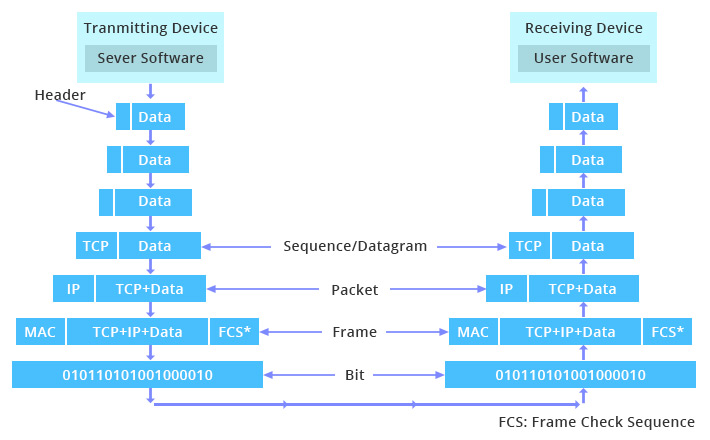
Data Encapsulation:
Packets are constructed in such a way that layers for each protocol used for a particular connection are wrapped around the packets, like the layers of skin on an onion.
At each layer, a packet has two parts: the header and the body. The header contains protocol information relevant to that layer, while the body contains the data for that layer which often consists of a whole packet from the next layer in the stack. Each layer treats the information it gets from the layer above it as data, and applies its own header to this data. At each layer, the packet contains all of the information passed from the higher layer; nothing is lost. This process of preserving the data while attaching a new header is known as encapsulation.
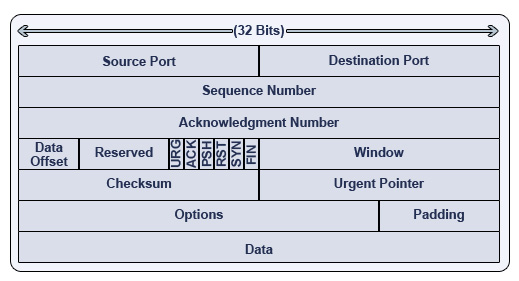
- TCP layer: Protocol data units (PDU) called a segment. The segment contains two parts: the TCP header and the TCP body.
- The TCP source port - a two-byte number, which specifies what client or server process the packet is coming from on the source machine
- The TCP destination port - just like the TCP source port
- The TCP flags field
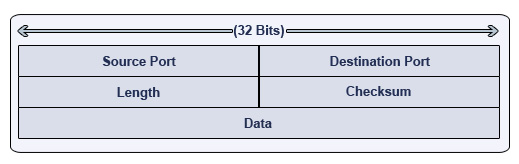
UDP Datagram is much less complicated.
- IP layer: PDU called a packet. Made up of two parts: the IP header and the IP body
- The IP source address - four bytes long.
- The IP destination address - just like.
- The IP protocol type - identifies the IP body as a TCP,UDP packet or an Internet Control Message Protocol (ICMP) packet etc.
- The IP options field - which is almost always empty, but which is where options like the IP source route and the IP security options would be specified if they were used for a given packet.
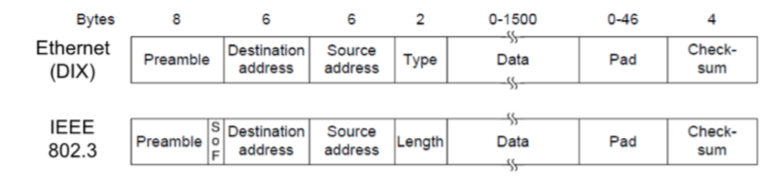
- Network Access layer: PDU called a frame. Frame consists of two parts: the Ethernet header and the Ethernet body.
- What kind of packet this is. Eg. an IP packet, an AppleTalk packet, a Novell packet etc.
- The Ethernet address of the machine that put the packet onto the network segment. I.e. the original source machine, or the last router in the path from the source machine to here.
- The Ethernet address of the packet’s destination on the network segment. I.e the destination machine, or the next router in the path from here to the destination machine.

Share this post
Twitter
Facebook
Reddit
LinkedIn
Email